The State of US Critical Infrastructure Control Systems
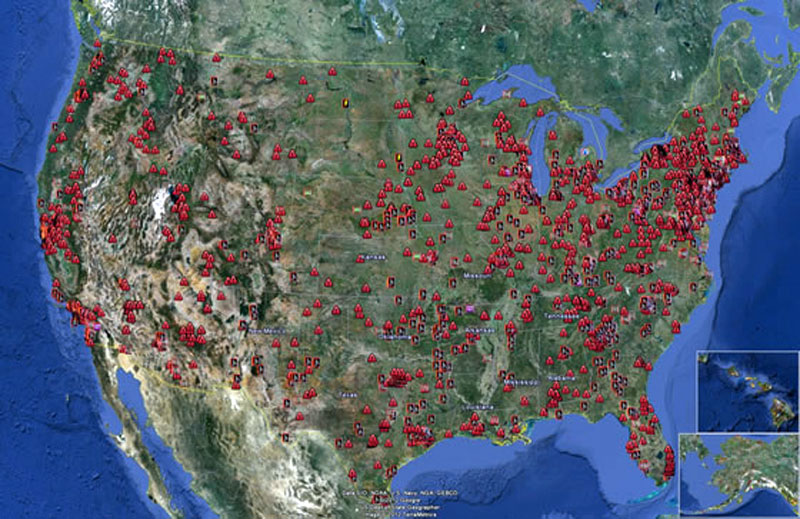
Just over a week ago, the United States’ Defense Secretary Leon Panetta gave a speech to business executives in New York City, sharing the government’s knowledge of “specific instances where intruders have successfully gained access to these control systems. We also know that they are seeking to create advanced tools to attack these systems and cause panic and destruction and even the loss of life.”
To instill the severity of the situation amongst attendees and citizens who would later hear of his cautioning across the country, Panetta confirmed several recent attacks against energy companies – including the use of an advanced, sophisticated virus attack that destroyed 30,000 computers owned by a large and well known oil company, Aramco.
Malicious software is not a new threat to industrial control systems. In fact, an extremely sophisticated computer worm named Stuxnet – that spreads via Microsoft Windows and targets Siemens industrial software and equipment – made headlines this summer for its ability to cripple a plant floor. This unusual and highly specialized malware attacked floor level control systems, which some analysts refer to as a form of corporate espionage.
The Stuxnet virus opened the eyes of our leadership team, our engineers, and our customers. With the rise of Bring Your Own Device (BYOD) and the increase in IT-based devices in industrial settings, security has risen from a fundamental requirement to an unparalleled concern. The standard methods of protection from hackers are just not keeping up with the pace that technologies targeted have evolved. Unfortunately, the industrial environment is still largely vulnerable.
There is a growing contingent of hackers across the globe that find opportunity and seek potential “pay days” by taking out competition, or making a statement against certain corporations. In fact, up to 80% of the Stuxnet virus infections were collateral damage, not the actual intended target. Now is the time to take a look your “defense in depth” strategy for IT security in your industrial environment, before it’s too late.
While the current state and security of control systems at each and every one of Patti Engineering’s customers may not be as imperative as that of the US critical infrastructure – and may not result in as treacherous an outcome for our country if breached – it is crucial that all systems are installed properly and run accurately. From asset/energy management, product distribution, manufacturing plants, to automation projects and more, it’s vital that productivity and efficiency of all systems are maintained. That’s how you comply with proper business practices and ensure profitability for the company.
As always, we’d love to hear from you. Are you concerned about the state and safety of the most critical US control systems? Are you confident in the security of your control systems? Please contact us if you would like us to conduct an evaluation of your systems to identify any potential security issues.
Related categories: Blog Company